Market signals
Three market signals showing why fragmented cybersecurity stacks now create operational risk.
Cybersecurity Impact
Outcomes
What changes in your operating reality — and how we prove it.
Impact metrics
- Control coverage across critical systems and processes (mapped to NIS2 / ISO 27001)
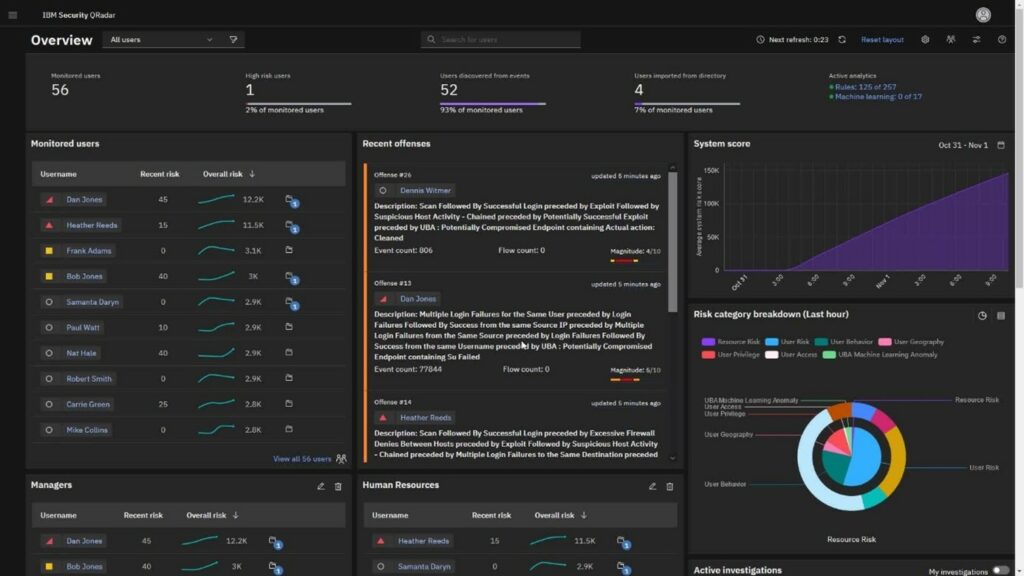
- MTTD / MTTR improvements supported by defined workflows and measurement cadence
- Alert quality (noise reduction, higher precision, better prioritization)
- Audit effort reduced through standardized evidence collection and review cycles
Reduce exposure and prove control coverage
NIS2 / ISO 27001-aligned controls embedded into operations — with ownership, evidence and continuous validation.
Improve detection and response performance
Better signal quality, faster triage and response execution — measured through MTTD/MTTR and incident workflow KPIs.
Lower incident cost and operational overhead
Prioritized remediation, automation where it reduces manual work, and a cleaner tooling posture with fewer blind spots.
Audit-ready evidence — continuously maintained
Evidence packs, logs, review records and control checks prepared as part of run-mode — not assembled the week before audit.
Featured Cybersecurity Solutions
Explore our comprehensive suite of security solutions with market-leading vendors
SIEM
Security Information and Event Management
Identity & Access Management
Centralized identity and authentication
Identity Governance
Access governance and lifecycle management
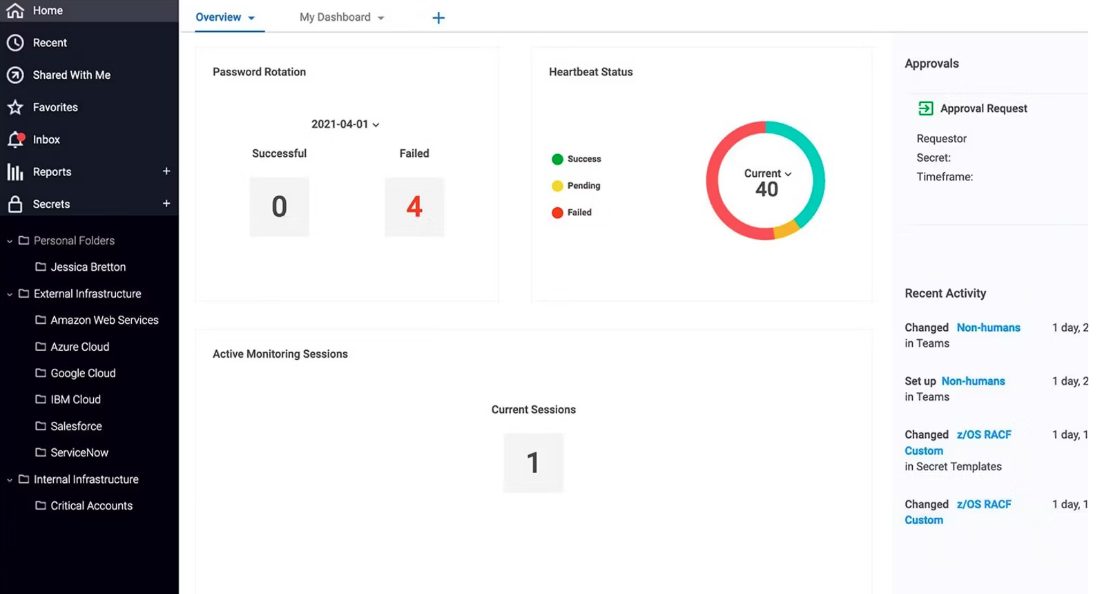
Secrets Management
Secure encryption and credential storage
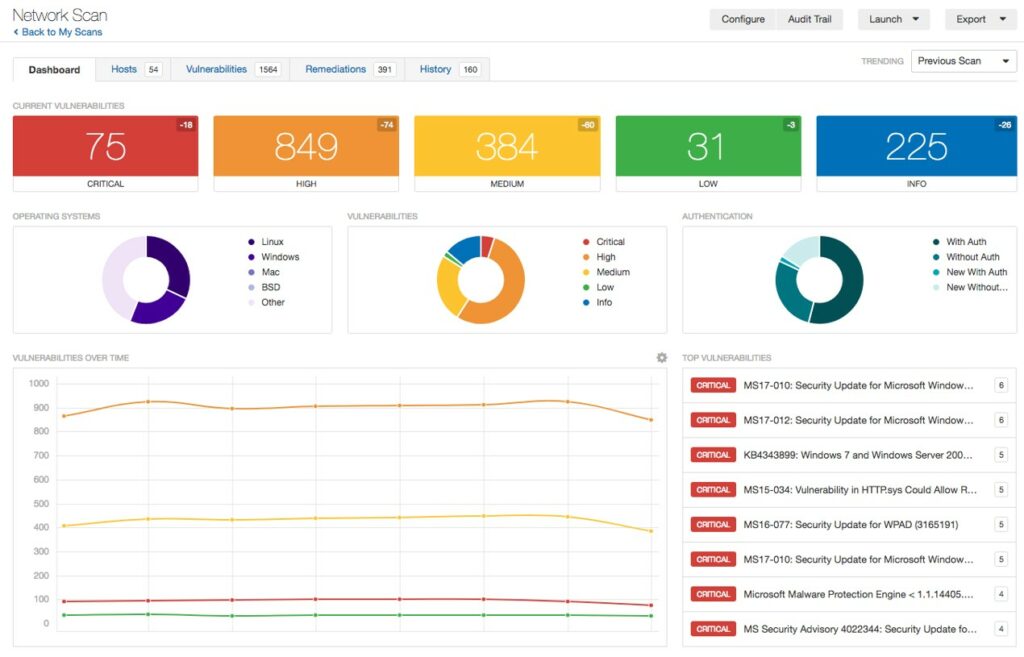
Vulnerability Management
Risk assessment and threat prioritization
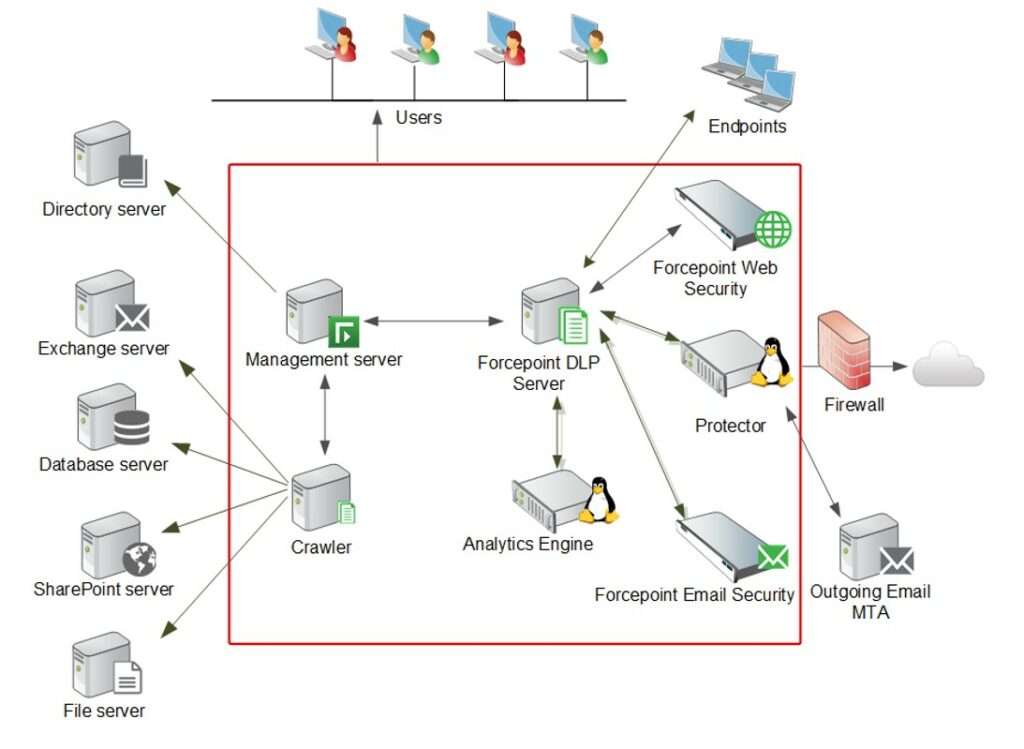
Data Loss Prevention
Endpoint and network data protection
Cybersecurity Audits
Structured security and compliance assessment
AI Governance
Risk, policy and controls for trusted AI adoption
PAM
Privileged Access Management
EDR
Endpoint Detection and Response
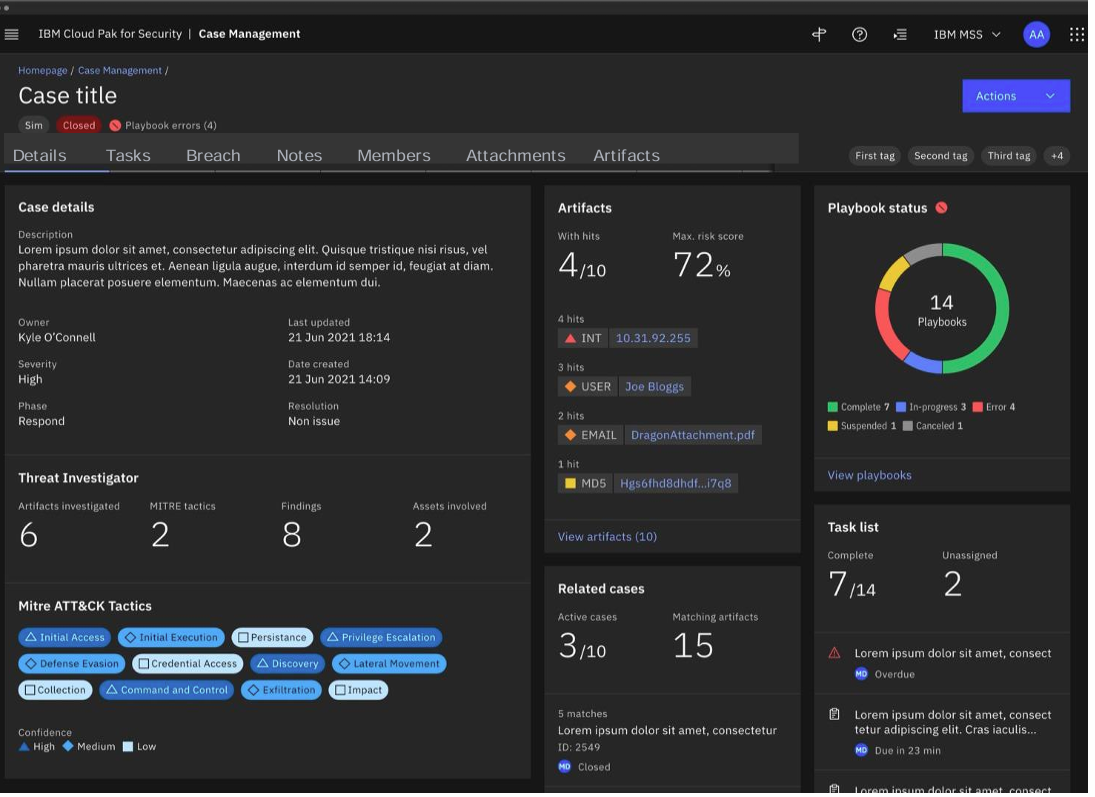
XDR
Extended Detection and Response
SOAR
Security Orchestration, Automation and Response
Trusted Expertise
10+ years leading security and transformation initiatives
Certified Partners
Implementation experts from IBM, Tenable, Forcepoint and more
Full Compliance Support
NIS2, ISO 27001, SOC, and custom regulatory frameworks
Comprehensive Services
From architecture design to 24/7 managed services support
Why Does Cybersecurity Drive Business Stability?
Cybersecurity protects core operations, data, and customer trust. It gives leadership measurable control over risk, compliance, and incident readiness.
How It Works in Practice
- Technology: continuous monitoring, identity control, data protection
- Processes: incident response, change control, risk reviews
- People: training, clear ownership, secure daily habits
- Compliance: NIS2, ISO/IEC 27001, SOC 2 with evidence
Key Challenges Organizations Face
- Faster automated attacks and delayed detection in fragmented environments
- Audit pressure (NIS2, ISO/IEC 27001, SOC 2) and evidence gaps
- Too many tools, too many alerts, and weak prioritization
- Identity risk: privileged accounts, cloud access, MFA lifecycle
- Third-party and supply-chain exposure across vendors
- Continuity pressure from ransomware, outages, and disruptions
What You Gain with Rhenai
- Clear risk visibility for faster and better decisions
- Higher resilience of systems, data, and user access
- Practical compliance: clear controls, processes, and KPIs
- Faster response through triage, correlation, and automation
- Stronger internal capability and security accountability
- Lower incident costs and less manual security work
Rhenai Delivery Model
Why Choose Rhenai?
We don't just deliver cybersecurity products — we design and implement end-to-end security architectures tailored to your business needs.
Certified Delivery
Implementation experts for IBM, Tenable, Forcepoint
Compliance-Ready Design
Built for NIS2, ISO 27001, SOC
Automation & Orchestration
Cross-platform workflows reducing manual effort
Managed & Advisory Services
Continuous optimization, monitoring and consulting
Cybersecurity for the Future of Work
Threats evolve — your defenses should too. Our solutions combine automation, intelligence and proven architecture to create a comprehensive security posture tailored to your risk profile.
Contact Us
.png)