OUR CORE CYBERSECURITY
DOMAINS & SOLUTIONS
TRANSFORM YOUR SECURITY OPERATIONS: NIS2 & ISO 27001-READY CYBERSECURITY FOR MODERN THREATS
In today’s environment of increasingly sophisticated digital threats and growing regulatory demands such as NIS2 and ISO 27001, cybersecurity is no longer just a technical layer—it’s a business-critical foundation. Our advanced cybersecurity solutions empower organizations to detect threats, respond to incidents, secure identities, and meet compliance requirements—quickly, intelligently, and at scale.
With our solutions, you can:
- Gain full visibility into your threat landscape with real-time detection
- Protect access and data using a zero-trust approach
- Ensure regulatory compliance, including NIS2 and ISO 27001
- Secure cloud, endpoint, and hybrid environments with integrated controls
Explore our key cybersecurity domains and solutions:
Enhance Detection & Response with IBM QRadar SIEM
IBM Security QRadar SIEM is an advanced security information and event management solution that provides full visibility into your IT environment. It collects, normalizes, and correlates data from a wide range of sources including firewalls, endpoints, cloud services, and applications. By leveraging built-in threat intelligence and user behavior analytics, QRadar detects anomalies and prioritizes the most critical incidents. Its real-time alerting and automated response workflows enable faster, more accurate threat mitigation. Scalable for on-premises, hybrid, and cloud deployments, QRadar is trusted by security teams to reduce noise and focus on what truly matters.
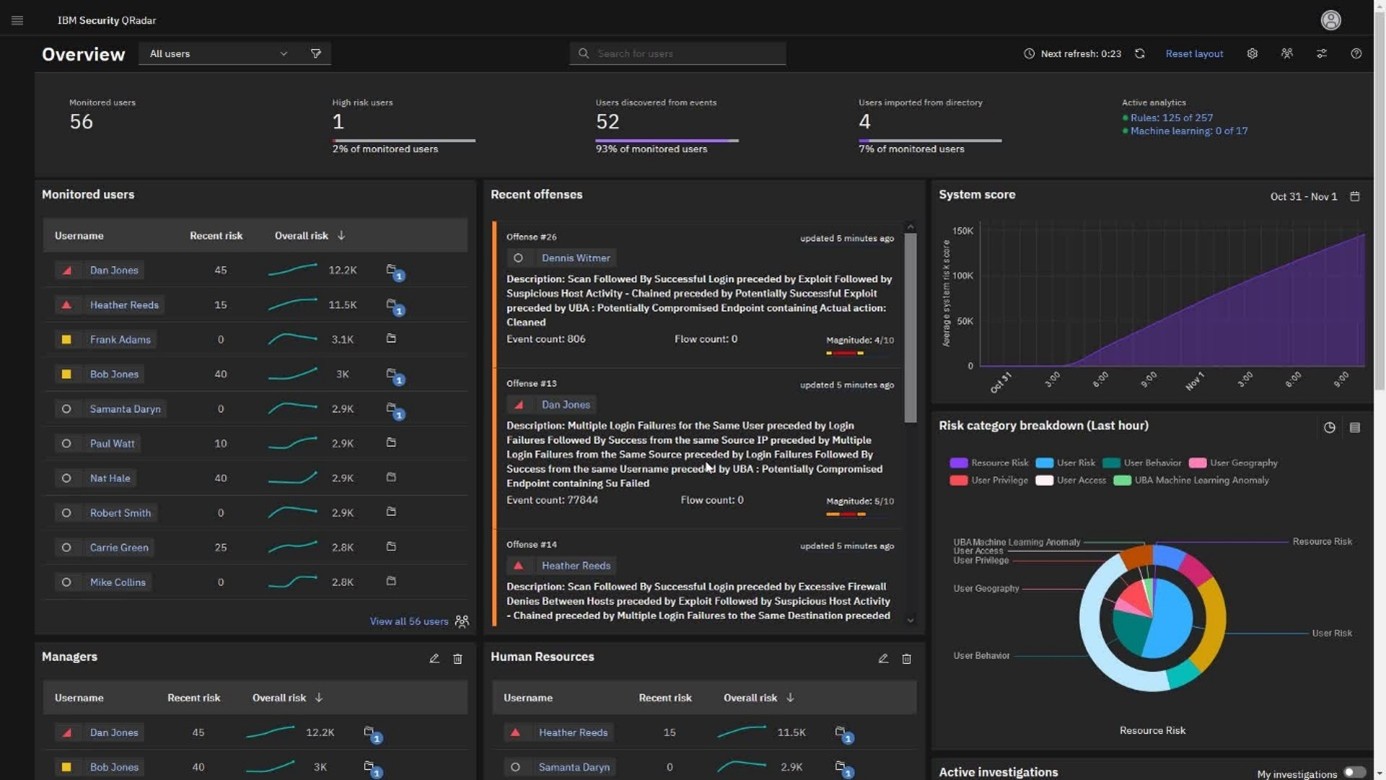
Boost Threat Visibility
Monitor and analyze events from firewalls, endpoints, and cloud systems in real time. QRadar correlates this data to uncover attack patterns and surface what truly matters.
Accelerate Incident Response
React faster with automated alerts and integrated workflows that prioritize the most critical threats.
Uncover Insider Risk
User Behavior Analytics (UBA) and threat intelligence integration identify unusual patterns and risky behaviors across your environment.
Key Benefits:
Secure Every Identity with IBM Identity and Access Management (IAM)
Adaptive access control designed for modern workforces. IBM Identity and Access Management (IAM) is a comprehensive solution that ensures the right individuals have secure and appropriate access to systems, applications, and data. It combines centralized identity governance with adaptive authentication methods such as Single Sign-On (SSO) and Multi-Factor Authentication (MFA). IBM IAM helps organizations enforce access policies, reduce identity-related risks, and meet regulatory requirements like NIS2 and ISO 27001. With features like role-based provisioning, access reviews, and threat-aware login behavior detection, it enhances both security and user experience. Designed for hybrid environments, IBM IAM scales easily across cloud and on-premises systems, supporting efficient onboarding and access control.
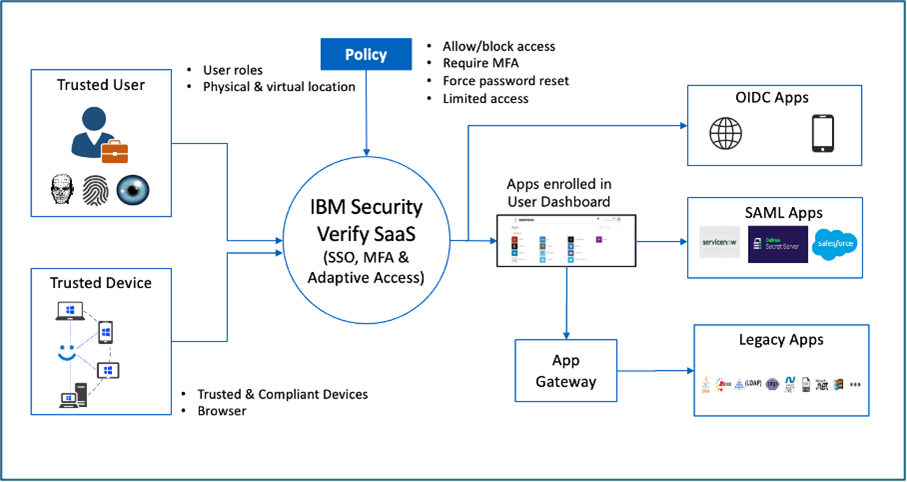
Key Benefits:
- Centralized Access Control: Streamlines management of user identities and access permissions across diverse systems and applications.
- Enhanced Security: Reduces risk with strong authentication methods like Single Sign-On (SSO) and Multi-Factor Authentication (MFA).
- Regulatory Compliance: Supports enforcement of policies such as NIS2 and ISO 27001, simplifying audits and governance.
- Adaptive Access Management: Dynamically adjusts access controls based on user behavior and contextual risk factors.
- Scalability and Flexibility: Easily deployable across on-premises, cloud, and hybrid environments to meet growing organizational needs.
Govern Access at Scale with IBM Verify Identity Governance
IBM Verify Identity Governance enables organizations to manage user access efficiently and securely at scale. It automates identity lifecycle processes through role-based provisioning and approval workflows, ensuring the right people have the right access. The solution enforces Separation of Duties (SoD) policies to reduce risk and maintain compliance. With risk-aware access reviews and detailed audit support, it simplifies governance and regulatory adherence. Designed for hybrid environments, IBM Verify Identity Governance helps businesses strengthen security while streamlining access management.
Automate Lifecycle Management
Provision and revoke access based on role, department, or project involvement.
Strengthen Policy Compliance
Prevent conflicts with SoD controls and streamline audit readiness through intelligent workflows.
Key Benefits:
- Role-based access and revocation
- Approval workflows and SoD enforcement
- Audit support and risk-aware reviews
- Ideal for: Compliance teams, risk managers, HR leaders
Centralize Secrets & Encryption with IBM HashiCorp Vault
The zero-trust solution for secure secret management and encryption. IBM HashiCorp Vault centralizes the management and protection of secrets such as passwords, tokens, and certificates across cloud and on-premises environments. It provides Encryption-as-a-Service (EaaS), enabling secure data encryption without complex integration. Vault supports dynamic secrets, tokenization, and key management protocols like KMIP to enhance system-to-system trust. Role-based access controls and comprehensive auditing ensure strict security and compliance. This solution empowers DevSecOps and infrastructure teams to securely manage sensitive information at scale.
Encrypt Everything, Trust No One
Store credentials, tokens, certificates, and keys securely—with full visibility and audit trails.
Build Secure-by-Design Pipelines
Integrate seamlessly with DevOps, microservices, and hybrid infrastructure.
Key Benefits:
- Centralized secret storage and EaaS
- Dynamic credentials and PKI
- KMIP support and RBAC
- Ideal for: DevSecOps, cloud architects, InfoSec leaders
Prioritize What Matters with Tenable Vulnerability Management
Tenable Nessus is a powerful vulnerability assessment tool designed to identify and prioritize security weaknesses across your IT environment. It continuously scans networks, systems, containers, and cloud assets to detect vulnerabilities before they can be exploited. With risk-based scoring and predictive analytics, Nessus helps security teams focus on the most critical threats. Its integration with SIEM, ITSM, and DevOps pipelines streamlines vulnerability management workflows. Trusted by CISOs and security engineers, Nessus enhances overall security posture by enabling proactive risk mitigation.
Risk-based exposure analysis across your attack surface. Tenable
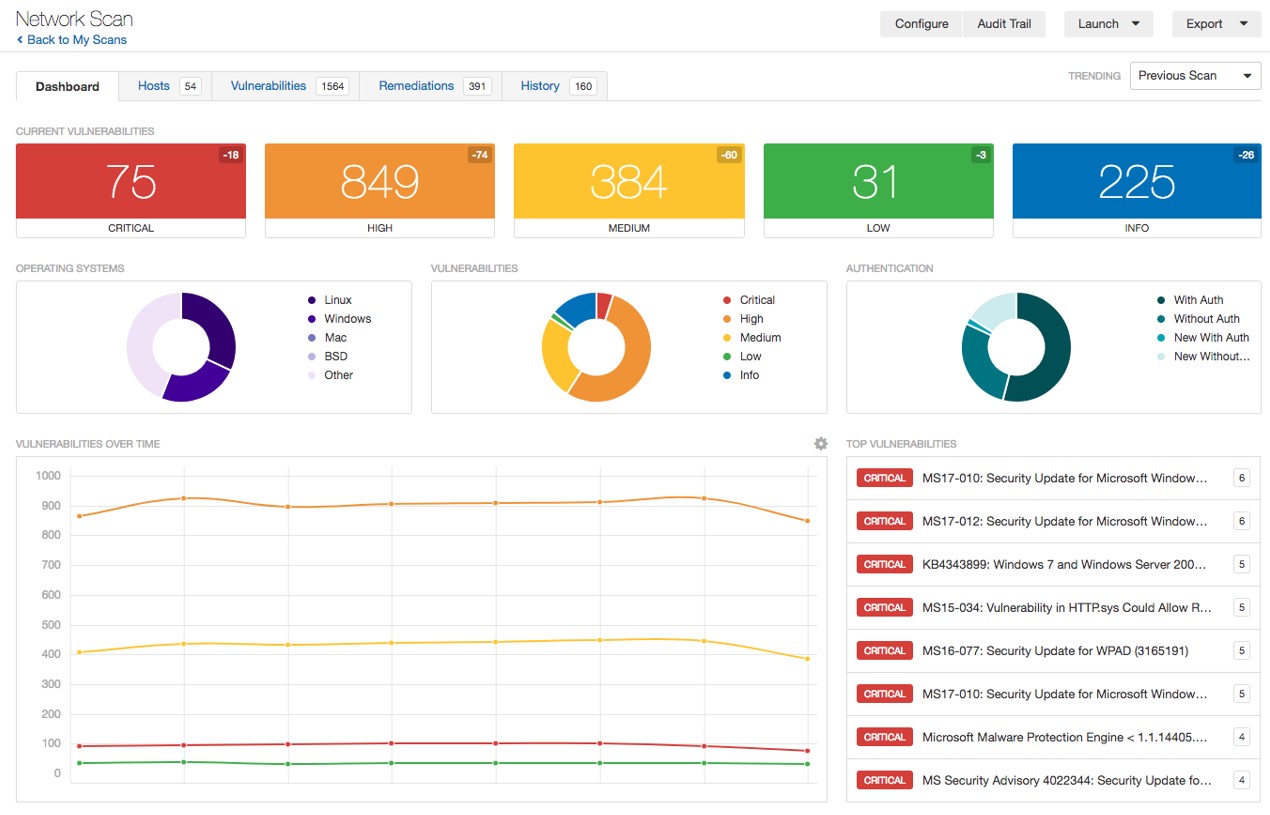
Know Your Assets, Know Your Risk
Discover and continuously assess cloud, container, endpoint, and IT assets.
Remediate with Context
Focus your efforts on the most business-critical vulnerabilities using predictive risk scoring.
Key Benefits:
- Asset visibility across hybrid environments
- CVSS and machine-learning-based prioritization
- Cloud-native and container security
- Ideal for: CISOs, security engineers, DevOps teams
Protect Data Where It Lives & Moves with Forcepoint DLP
Forcepoint Data Loss Prevention (DLP) is a comprehensive solution designed to protect sensitive data wherever it resides—on endpoints, networks, cloud applications, and email. It uses human-centric, behavior-aware technology to understand how users interact with data, reducing the risk of insider threats. Forcepoint DLP accelerates compliance with over 370 regulatory policies across 83 countries through adaptive protection and machine learning. Features like fingerprinting, coaching dialogs, and risk-based incident prioritization help organizations detect and prevent data leaks effectively. Ideal for compliance teams and data protection officers, Forcepoint DLP ensures sensitive information stays secure while enabling business continuity.
Behavior-aware, human-centric data protection.
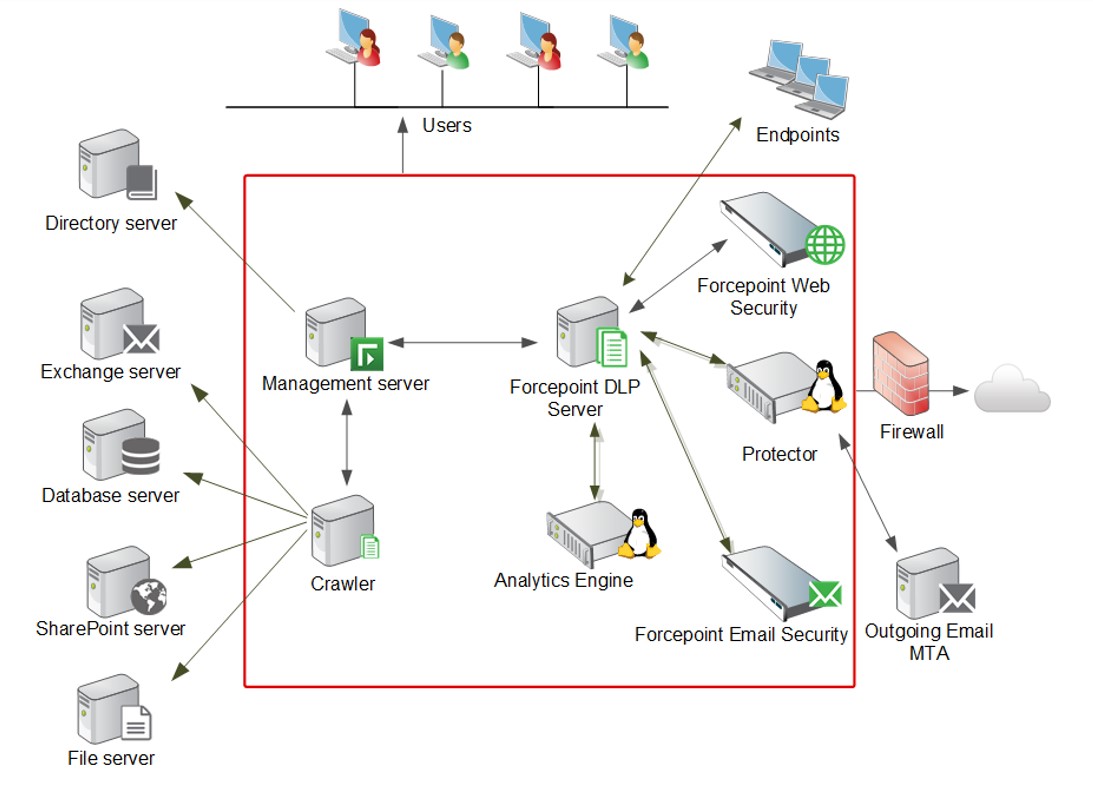
Understand user behavior to prevent accidental or malicious leaks—on endpoints, in emails, across apps or networks.
Meet Global Compliance at Scale
Prebuilt policies for over 370+ regulations help you stay compliant across jurisdictions.
Key Benefits:
- Endpoint, network & cloud DLP
- ML-based fingerprinting & OCR
- Compliance with GDPR, ISO 27001, HIPAA
- Ideal for: Data Protection Officers, compliance teams, IT risk managers
CYBERSECURITY FOR THE FUTURE OF WORK
Cyber threats are evolving—your defenses should too. Our solutions combine automation, intelligence, and proven architecture to create a robust security ecosystem tailored to your organization’s risk profile.
Whether you’re securing remote workforces, modernizing SOC operations, or preparing for compliance audits (NIS2, ISO 27001, SOC 2), we help you move faster and safer.
Contact
WHY CHOOSE RHENAI?
At Rhenai, we don’t just deliver cybersecurity products — we design and implement end-to-end security architectures tailored to your business needs. Our certified experts in IBM, Tenable, and Forcepoint technologies ensure your environment is protected, optimized, and compliant with standards like NIS2, ISO 27001, and SOC 2. We integrate automation and orchestration across tools to reduce manual effort, while our managed services and ongoing consulting provide continuous improvement and risk visibility. With Rhenai, you gain a strategic partner focused on long-term security, operational efficiency, and regulatory resilience.
We go beyond licensing—we architect your security success.
- Certified Delivery: IBM, Tenable, Forcepoint implementation experts
- Compliance-Ready Designs: Built for NIS2, ISO 27001, SOC 2 and more
- Automation & Orchestration: Cross-platform workflows to reduce manual effort
- Managed & Advisory Services: Continuous optimization, monitoring, and consulting
- Strategic Risk Management: We align cybersecurity with your business outcomes
